(Minghui.org) United States President Donald Trump issued an executive order on January 5, banning 8 Chinese software applications with ties to the Chinese Communist Party (CCP). The order will be carried out by the Secretary of Commerce, the Attorney General, the Director of National Intelligence, and the Secretary of the Treasury. Transactions related to the eight apps are to be prohibited within 45 days of the order.
This order, “Executive Order Addressing the Threat Posed By Applications and Other Software Developed or Controlled By Chinese Companies,” is available on the White House website. The 8 apps are: Alipay, CamScanner, QQ Wallet, SHAREit, Tencent QQ, VMate, WeChat Pay, and WPS Office.
These mobile and desktop applications “continue to threaten the national security, foreign policy, and economy of the United States,” states the Order, and, “action must be taken to address the threat posed by these Chinese connected software applications.”
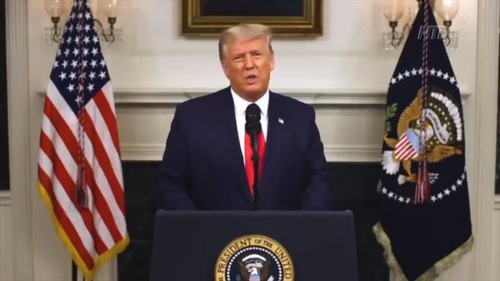 U.S. President Trump issued an executive order on January 5 that bans 8 mobile and desktop applications connected to the Chinese Communist Party (CCP).
U.S. President Trump issued an executive order on January 5 that bans 8 mobile and desktop applications connected to the Chinese Communist Party (CCP).
Addressing Threat from the CCP
This Order is authorized based on the U.S. Constitution and other laws, including the International Emergency Economic Powers Act (50 U.S.C. 1701 et seq.) (IEEPA), the National Emergencies Act (50 U.S.C. 1601 et seq.), and section 301 of title 3, United States Code.
Due to the “pace” and “pervasiveness” of the spread in the United States of these applications and other software developed or controlled by persons in the People’s Republic of China, including Hong Kong and Macau (China), “additional steps must be taken to deal with the national emergency with respect to the information and communications technology and services supply chain declared in Executive Order 13873 of May 15, 2019 (Securing the Information and Communications Technology and Services Supply Chain),” the Order continued.
The term “connected software application” refers to “software, a software program, or group of software programs, designed to be used by an end user on an end-point computing device and designed to collect, process, or transmit data via the Internet as an integral part of its functionality.”
Through personal electronic devices such as smartphones, tablets, and computers, Chinese connected software applications can access and capture vast swaths of information from users, including sensitive personally identifiable information and private information. “This data collection threatens to provide the Government of the People’s Republic of China (PRC) and the Chinese Communist Party (CCP) with access to Americans’ personal and proprietary information — which would permit China to track the locations of Federal employees and contractors, and build dossiers of personal information,” states the Order.
It has been an ongoing effort by the CCP to steal U.S. data, which clearly shows it intends to use bulk data collection to advance China’s economic and national security agenda. For example, the 2014 cyber intrusions of the Office of Personnel Management of security clearance records of more than 21 million people were carried out by Chinese agents. In 2015, a Chinese hacking group breached the United States health insurance company Anthem, which affected more than 78 million Americans. Furthermore, the Department of Justice indicted members of the Chinese military for the 2017 Equifax cyber intrusion, which compromised the personal information of almost half of all Americans.
Because of these risks, many executive departments and agencies have prohibited the use of Chinese connected software applications and other dangerous software on Federal Government computers and mobile phones. But these actions “are not enough given the nature of the threat from Chinese connected software applications.” For example, the Government of India has banned the use of more than 200 Chinese connected software applications throughout the country. India’s Ministry of Electronics and Information Technology asserted in a statement that the applications were “stealing and surreptitiously transmitting users’ data in an unauthorized manner to servers which have locations outside India.”
“The United States has assessed that a number of Chinese connected software applications automatically capture vast swaths of information from millions of users in the United States, including sensitive personally identifiable information and private information, which would allow the PRC and CCP access to Americans’ personal and proprietary information,” continued the Order. “The United States must take aggressive action against those who develop or control Chinese connected software applications to protect our national security.”
Secretary of Commerce: Implementation in Progress
These 8 applications were identified by the U.S. Department of Commerce. The Order also requests the heads of involved agencies to “provide, in their discretion and to the extent permitted by law, such resources, information, and assistance to the Department of Commerce as required to implement this order, including the assignment of staff to the Department of Commerce to perform the duties described in this order.”
Wilbur Ross, Secretary of Commerce, issued a statement the same day supporting the Order. “Consistent with the authorities designated to the Secretary of Commerce from the President, I have directed my Department to begin implementing the E.O.’s directives, including identifying prohibited transactions related to certain Chinese connected software applications,” he wrote.
“I stand with President Trump’s commitment to protecting the privacy and security of Americans from threats posed by the Chinese Communist Party, and the Department of Commerce will leverage the authorities of the E.O. to continue our mission to secure the nation, the economy, and the people of the United States,” Ross continued.
Deputy National Advisor: “What Evil Fears Most Is the Publicly Spoken Truth”
Matt Pottinger, U.S. Deputy National Advisor, gave a speech on October 23 during a conference hosted by Policy Exchange in London. The speech, “The Importance of Being Candid” was given in Chinese and its English version is available on the White House website.
Through foreign interference, collection of big data, the United Front, and hijacking individuals and nations, the CCP is harming free society and threatening the world, he said.
One example is the CCP’s United Front Work system, referred to as a “magic weapon” since Mao Zedong’s era. With support by 90 million CCP members for its activities, “the United Front Work Department alone has four times as many cadres as the U.S. State Department has foreign-service officers,” Pottinger explained. “But instead of practicing diplomacy with foreign governments—the Chinese foreign ministry handles that—the United Front gathers intelligence about, and works to influence, private citizens overseas. The focus is on foreign elites and the organizations they run. Think of a United Front worker as a cross between an intelligence collector, a propagandist, and a psychologist.”
Pottinger said that the United Front work affects both U.S. officials and ordinary citizens. “After all, the raw material for psychologists is data about their patients. The Party is compiling digital dossiers on millions of foreign citizens around the world. The exposure last month of a Chinese database on at least 2.4 million people around the world—including many of us on this call—speaks to the Party’s sheer ambition to wed traditional Leninist techniques with powerful new tools of digital surveillance,” he added.
“Assembling dossiers has always been a feature of Leninist regimes. The material is used now, as before, to influence and intimidate, reward and blackmail, flatter and humiliate, divide and conquer. What’s new is how easy we’ve made it for autocrats to accumulate so much intimate data about ourselves—even people who’ve never set foot in China.” He continued, “We leave our intellectual property, our official documents, and our private lives on the table like open books. The smart phones we use all day to chat, search, buy, view, bank, navigate, network, worship and confide make our thoughts and actions as plain to cyber spooks as the plumes of exhaust from a vintage double-decker bus.”
One example is Shenzhen Zhenhua Data Information Technology Co, a company that builds these dossiers known as “psychological warfare,” as described by its CEO. Zhenhua harvests and organizes public and private data about Americans for exploitation by its clients, namely, organs of the Chinese security apparatus, states its website.
“The dossiers Zhenhua is compiling include people in virtually every country on earth, no matter how small. They include members of royal families and members of parliament, judges and clerks, tech mavens and budding entrepreneurs, four-star admirals and the crewmembers of warships, professors and think-tankers, and national and local officials,” Pottinger explained. “They also include children, who are fair game under Beijing’s rules of political warfare. No one is too prominent or too obscure.”
“Zhenhua isn’t a particularly large or sophisticated actor in the United Front world. It may even be acting opportunistically, because it thinks the Party will reward it. Far more powerful tech firms, including famous Chinese app developers, play a much bigger role in this kind of work,” he continued. “The Chinese Communist Party has reorganized its national strategy around harnessing that digital exhaust to expand the Party’s power and reach.”
All these are strategic steps to achieve the CCP’s expansion and dominance to advance its communism ideology. “This is where United Front propaganda and psychology come into play. The Party’s overseas propaganda has two consistent themes: ‘We own the future, so make your adjustments now.’ And: ‘We’re just like you, so try not to worry.’ Together, these assertions form the elaborate con at the heart of all Leninist movements,” Pottinger added.
Despite these challenges, Pottinger said institutionalized evil can be enormously powerful, but also enormously fragile. “It is compulsively aggressive and ultimately self-destructive. It senses its own moral absurdity. It knows it is a raft on a sea of ontological good,” he concluded. “What evil fears most is the publicly spoken truth.”
Category: Media Reports



